|
Technical Principle Multi-dimensional Security Protection, Born For Host Security The computer architecture determines that any data needs to be processed by the CPU, and its data needs to be stored through memory. In theory, a security solution based on monitoring CPU instruction set and memory can effectively prevent all threats. Different from the conventional security products only running in the application layer or kernel layer, MDPS can provide organic combination of three-dimensional protection in the application layer, kernel layer and hardware layer. |
|
|
Technical Principle Multi-dimensional Security Protection, Born For Host Security The computer architecture determines that any data needs to be processed by the CPU, and its data needs to be stored through memory. In theory, a security solution based on monitoring CPU instruction set and memory can effectively prevent all threats. Different from the conventional security products only running in the application layer or kernel layer, MDPS can provide organic combination of three-dimensional protection in the application layer, kernel layer and hardware layer. |
Core Security Protection
|
0-day vulnerability Behavior analysis and memory monitoring based on machine learning can prevent a large number of enterprise level threat vulnerabilities. |
|
Fileless attacks Compared to the complete failure of traditional security software, the Anxin Shenjia can accurately identify and protect against fileless attacks. |
|
Buffer overflow attacks Efficient protection stack memory overflow, protect the security of program data. |
|
DLL injection The protection process is not illegally injected, effectively preventing the DLL file from being hijacked, tampering, etc. |
|
ROP gadgets Powerful code protection technology can accurately identify and block the construction of malicious code. |
|
Side-channel attacks It can protect against attacks such as Spectre and Meltdown, and avoid user data breaches. |
|
Corruption of Strongly protect configuration data from tampering and avoid configuration data corruption. |
|
Malware Killing Based on behavior to detect viruses and Trojans, Anxin has strong ability to kill and clear. |
Born For The Host Security
Powerful memory data probe capability can solve deeper security problems and risks.
| Core Strengths | Anti-Virus | Adaptive | Host Hardening | MDPS |
|---|---|---|---|---|
| Prevent Memory Data Breach |

|

|

|

|
| Defense Unknown/ Fileless Attacks |

|

|

|

|
| No Signature Rule Upgrade Required |

|

|

|

|
| Automatically Execution Correctly |

|

|

|

|
| Protect from 0-day vulnerability exploit |

|

|

|

|
| No Need to Adapt/Modify Password |

|

|

|

|
| No Hardware/System Conflicts |

|

|

|

|
| Minimal impact on Performance |

|

|

|

|
| File System Monitoring |

|

|

|

|
| Low False Positive Rate |

|

|

|

|
Support For Multiple Deployment Modes

Local Deployment
Local deployment is a common network deployment environment. It adopts a purely soft architecture and can be quickly deployed in physical machines and virtual machines to achieve efficient management of security and operation and maintenance.
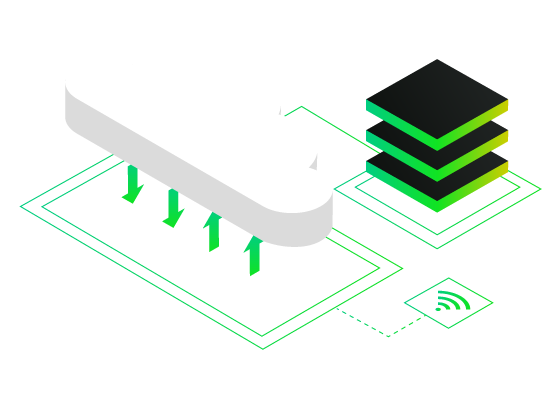
Private Cloud Deployment
The private cloud deployment mode can meet the enterprise's more secure and flexible business expansion ability, and facilitate enterprise management.
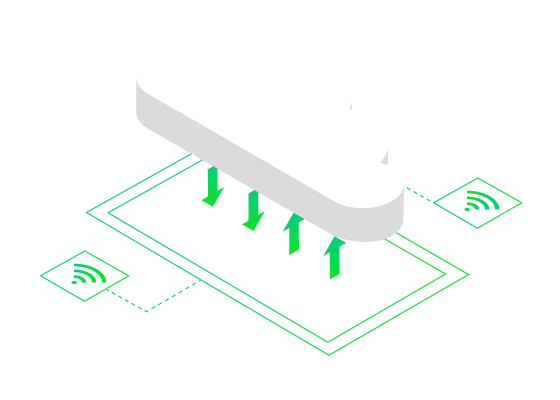
Public Cloud Deployment
Public cloud deployment is lightweight and fast deployment, supporting Windows and Linux system security protection. It can be deployed in a few minutes and security is activated immediately.

Local Deployment
Local deployment is a common network deployment environment. It adopts a purely soft architecture and can be quickly deployed in physical machines and virtual machines to achieve efficient management of security and operation and maintenance.
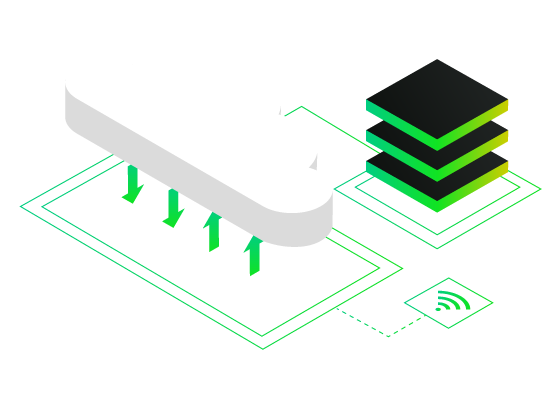
Private Cloud Deployment
The private cloud deployment mode can meet the enterprise's more secure and flexible business expansion ability, and facilitate enterprise management.
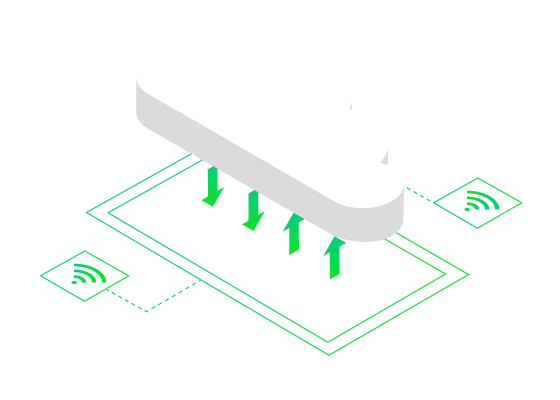
Public Cloud Deployment
Public cloud deployment is lightweight and fast deployment, supporting Windows and Linux system security protection. It can be deployed in a few minutes and security is activated immediately.